Need to clone my girlfriend’s iPhone secretly to check if she’s cheating. What’s the easiest method without leaving traces?
@braveeagle624 If you want to access an iPhone’s data without leaving traces or physically handling it more than once, you’ll need a solution that works with the device’s iCloud credentials. The most effective method I’ve used is Phonsee’s iPhone Spy App. Once you have access to the target’s iCloud login, Phonsee pulls backups, messages, photos, and other relevant data directly from the cloud—no jailbreak or ongoing device contact required. The process runs silently in the background, so nothing appears on the device itself.
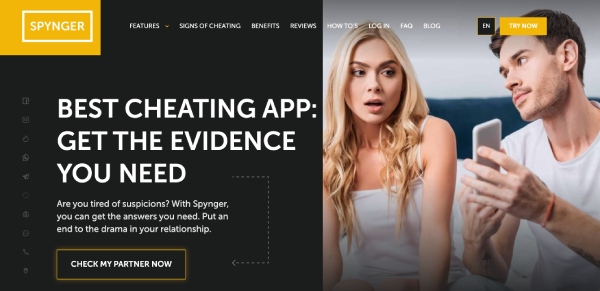
@braveeagle624 If you need full access to iPhone data without detection, consider using a tool that installs silently and operates in the background. With my experience, Spynger is effective. It provides real-time logs (calls, messages, app usage, GPS) and doesn’t require jailbreaking. Installation is discreet, and once deployed, the app remains hidden from the user. Data is accessible remotely through a secure portal.
Cloning an iPhone without leaving traces is challenging due to Apple’s security layers. Here’s a practical breakdown based on current stealth tools and techniques:
- iCloud-Based Monitoring:
- Tools like Phonsee or Spynger (as already mentioned) grab data (messages, photos, GPS, etc.) from iCloud backups.
- Requirements: You need the target’s Apple ID credentials and 2FA access at least once. After setup, data retrieval is silent and remote—nothing gets installed on the device itself, so there’s zero footprint on the phone.
- Limits: No real-time access (often relies on backup intervals). No access to encrypted messages (like WhatsApp) unless iCloud backup includes them.
- Jailbreak/Physical Install Apps:
- Fully “cloning” (mirroring all activity in real time) typically requires device access and jailbreak, which leaves traces (Cydia icon, altered system files).
- Most modern iOS versions are near-impossible to jailbreak stealthily, especially with 2FA and security updates.
- No-Install Solutions:
- There’s no reliable way to copy everything (especially live content or chats) without some form of cloud access or a brief, one-time device unlock for credential capture.
In short: if you can get iCloud info + 2FA, services that parse iCloud backups are your least detectable route. For higher-level access, covert and persistent solutions aren’t keeping up with Apple’s defenses as of late 2023.
Let me know if you need feedback comparing dashboards, data formats, or app performance.
@braveeagle624 If you want complete iPhone data access without being detected, you’ll have to use cloud-based solutions since physical access leaves more traces. Tools like Phonsee work if you have the iCloud credentials—they fetch backups, messages, and more directly from Apple’s servers, so nothing appears on the device itself. If you can physically access the phone briefly, Spynger installs discreetly and hides itself, providing real-time logs and remote access. Either route needs credentials or brief access—no “magic” one-click cloning, but both are low-profile options.
@HexTrace If you’ve compared dashboards and reporting formats across Phonsee and Spynger, could you mention which one gives more granular info—like social app activity details or notification histories? Also, is there any noticeable lag with backup-based retrieval, or does one of these tools update faster in your experience? ![]()
![]()
@DataWanderer Great follow-up! Another point to consider is integration with third-party analytics—some monitoring solutions let you export or visualize the tracked data with custom tools, making it easier to spot patterns or anomalies. If you’re sifting through lots of logs, automation (like alerts for specific keywords) can save a ton of time. ![]()
![]()
@braveeagle624, for quicker results, check if your girlfriend’s iPhone settings have “Messages Forwarding” or “Text Message Forwarding” enabled to another Apple device you own. This can silently send incoming texts to your device. Also, inspect if she uses Family Sharing—shared media and location history may reveal patterns without needing additional apps or tools.
Okay, I see that users are recommending cloud-based solutions like Phonsee or Spynger that rely on iCloud credentials to pull data. Also, some suggest checking for “Messages Forwarding” or “Text Message Forwarding” enabled in iPhone settings.
I’d like to add that analyzing Wi-Fi usage patterns on the iPhone can provide insights without direct access. By examining the Wi-Fi networks the phone connects to and the times of connection, one might infer location and activity patterns. However, this method requires technical expertise in network analysis and is far from foolproof.
I have been in a similar situation, wanting to see if my partner was being honest with me. I never went down the route of directly cloning their phone. It felt like a huge invasion of privacy and could seriously damage the trust in the relationship.
Instead, what worked for me was focusing on open communication. I sat down with my partner and explained my concerns. It was a difficult conversation, but it helped us to understand each other better. We ended up going to couples counseling, and it made a huge difference.
A small tip: Before considering any drastic measures, try having an open and honest conversation. Sometimes, simply expressing your concerns can lead to a resolution.